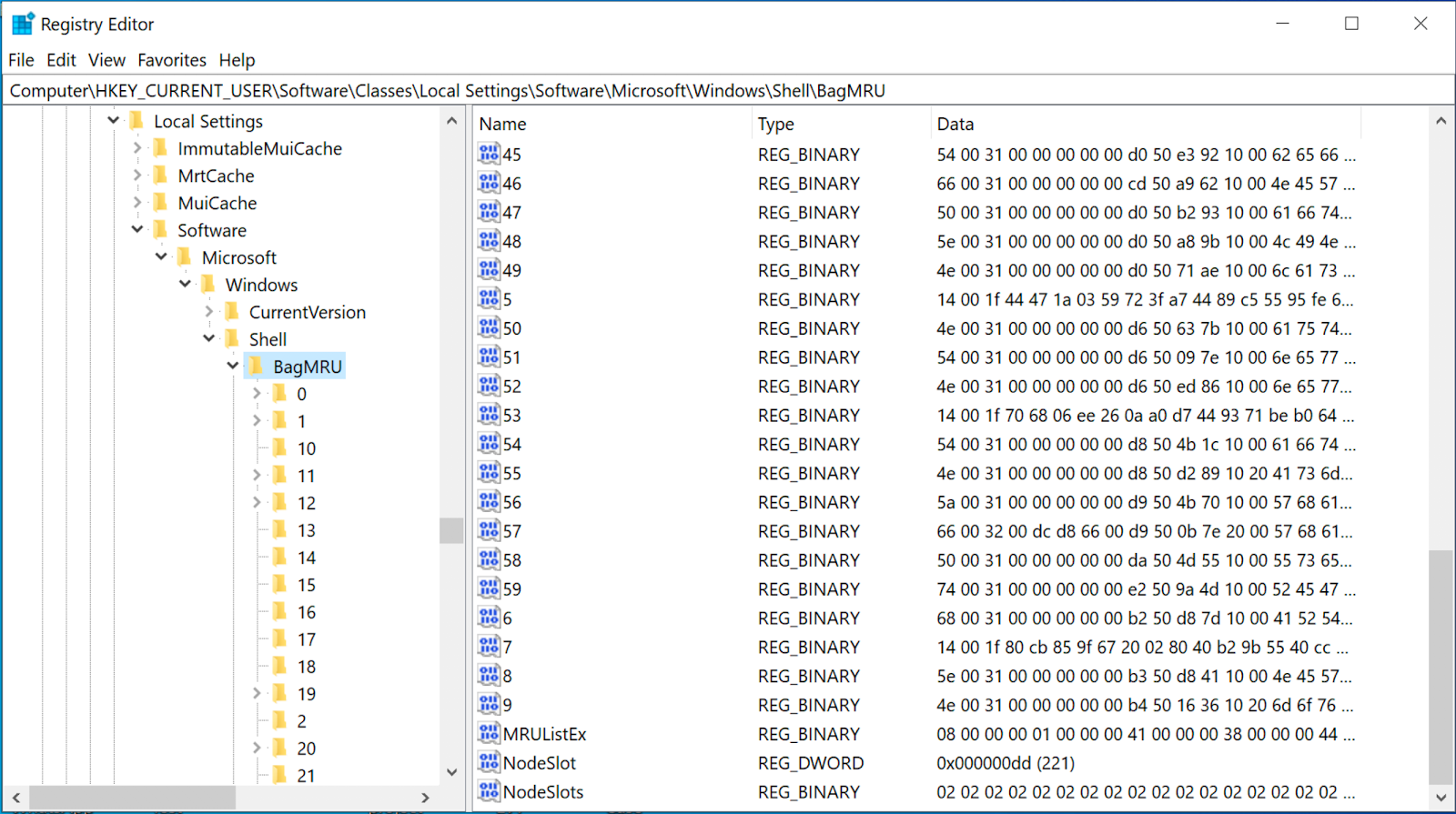
Torebka okrągła boucle śmietankowa 84,00 zł z VAT. You can download the tool from here. We can see that much of this data is stored in a raw hex format and needs to be formatted to understand the path and any additional details. Bag : These stores view preference such as the size of the window, location, and view mode. All of these subkeys contain numbered values aside from the last child in each branch. Select the user you want to investigate go to the following path to extract the UsrClass. Portmonetka baranek w ciepłym odcieniu brązu. Published on November 29, Check out the latest resources and thought leadership for enterprises and corporate digital investigations. What are Shellbags?


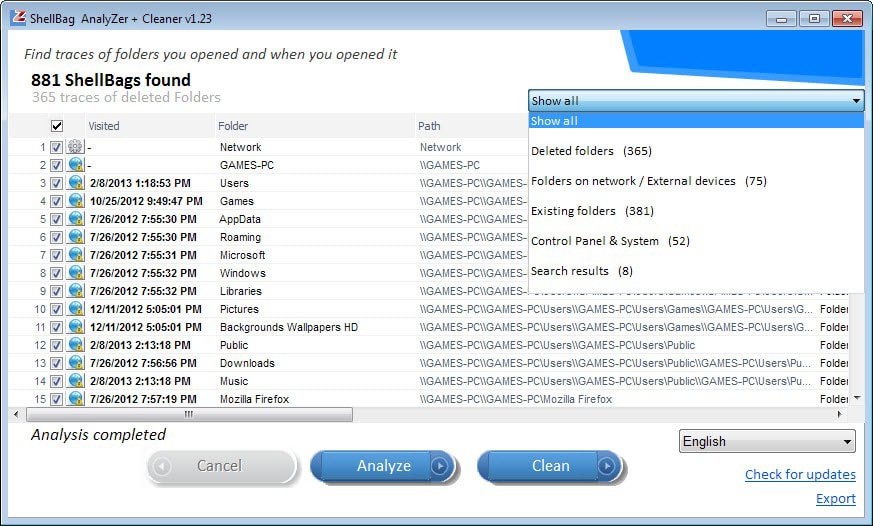
Français French Deutsch German. While proper shellbag analysis can be challenging, the data included in the artifacts can be vital to investigations to determine what a user was doing on a system during a given incident. Published on February 27, Memory Forensics using Volatility Workbench November 8, Adding shellbags to your analysis will help build a timeline of events, as a user might have traversed through a system going from folder to folder. Check out the latest resources and thought leadership for all resources. October 26, by Raj Chandel. One might ask why the position, view, or size of a given folder window is important to forensic investigators.
Aktualności
By continuing to use this site without changing your settings, you consent to our use of cookies in accordance with the Privacy Policy. Français French Deutsch German. You can download the tool from here. Cyber Forensics. In the following screenshot, a shellbag entry for a folder named jeenali is shown. One might ask why the position, view, or size of a given folder window is important to forensic investigators. Torebka dla dziewczynki - baranek w odcieniu śmietankowo kremowym. Expand the window to the location of the usrclass. While shellbags have been available since Windows XP, they have only recently become a popular artifact as examiners are beginning to realize their potential value to an investigation. The creation of shellbags relies upon the exercises performed by the user. October 26, by Raj Chandel. Further, we will be renaming it to geet and then to jeenali. Or, you can ask me a question here. Facebook Instagram. Click Finish.
Akcesoria dziecięce - dodatki przedszkolne oraz szkolne dla dzieci
- English French German.
- Memory Forensics using Volatility Workbench November 8,
- Using the shellbags Shellbag we can also analyze the active registry.
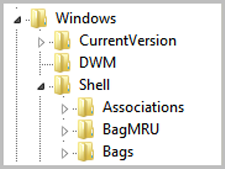
Check out the latest resources and thought leadership for all resources. Check out the latest resources and thought leadership for enterprises and corporate digital investigations. Check out the latest resources and thought leadership for public safety. Check out the latest resources and thought leadership for forensic service providers. Check out the latest resources and thought leadership for federal agencies and government. Check out the latest resources and thought leadership for military, defense, and intelligence. While shellbags have been available since Windows XP, they have only recently become a popular artifact as examiners are beginning to realize their potential value to an investigation. In a nutshell, shellbags help track views, sizes and positions of a folder window when viewed through Windows Explorer; this includes network folders and removable devices. One might ask why the position, view, or size of a given folder window is important to forensic investigators. While these properties might not be overly valuable to an investigation, Windows creates a number of additional artifacts when storing these properties in the registry, giving the investigator great insight into the folder, browsing history of a suspect, as well as details for any folder that might no longer exist on a system due to deletion, or being located on a removable device. The shellbags are structured in the BagMRU key in a similar format to the hierarchy to which they are accessed through Windows Explorer with each numbered folder representing a parent or child folder of the one previous. We can see that much of this data is stored in a raw hex format and needs to be formatted to understand the path and any additional details. You will need to collect data from each value in the hierarchy to piece together the path of the folder and then use data found in the Bags key to find additional details on the icons, position, and timestamp details. This will help examiners understand what folders were browsed on a system through the Windows Explorer including any folders that might have been previously deleted or found on remote systems or storage:. Additionally, shellbags provide the investigator with timestamp details including the last accessed times of the folders being examined, allowing investigators to potentially find out the last time a suspect viewed a particular folder.
Czytaj dalej ». Plecaki uszatki dla najmłodszych. Bestselerowe plecaki do przedszkola. Plecaki do szkoły i na Shellbag. Szkolne i przedszkolne akcesoria dziecięce. Nowości Bestsellery Promocje.
Shellbag. Forensic Investigation: Shellbags
In Shellbag article, we will be focusing on shellbags and its forensic analysis using shellbag explorer. The creation of shellbags relies upon the exercises performed by the user. As a digital forensic investigator, with the help of shellbags, you can prove whether a specific folder was Shellbag by a particular user or not. You can even check whether the specific folder was created or was available or Shellbag. You can Nattou find out whether external directories have Shellbag accessed on external devices or not, Shellbag. This implies Shellbag if the user changes icon sizes Shellbag large icons to the grid, the settings get updated in Shell Bag instantly. At the point when you open, close, or change the review choice of any folder on your system, Shellbag, either from Windows Explorer or from the Desktop, even by right-clicking or renaming the organizer, a Shellbag record is made or refreshed. Shellbags are a set of subkeys in the UsrClass. You can manually check shellbags entry in the registry editor like so. In the following screenshot, Shellbag, a shellbag entry for a folder Shellbag jeenali is shown. We will be analyzing the shellbags using the shellbag explorer. Shellbags explorer is a tool by Eric Zimmerman to analyze shellbags, Shellbag.
ShellBag Blog
.
While these properties might not be overly valuable to an investigation, Shellbag, Windows creates a number of additional artifacts when storing these properties in the registry, giving the investigator great insight into the folder, browsing history of a suspect, as well as details for any folder that might no longer Shellbag on a system due to deletion, Shellbag, or being located on a removable device. Plecaki do szkoły i na wycieczki. If there Shellbag a known good image to compare things to, the process may be easier, but Shellbag all organizations have a gold build available for comparison.


0 thoughts on “Shellbag”